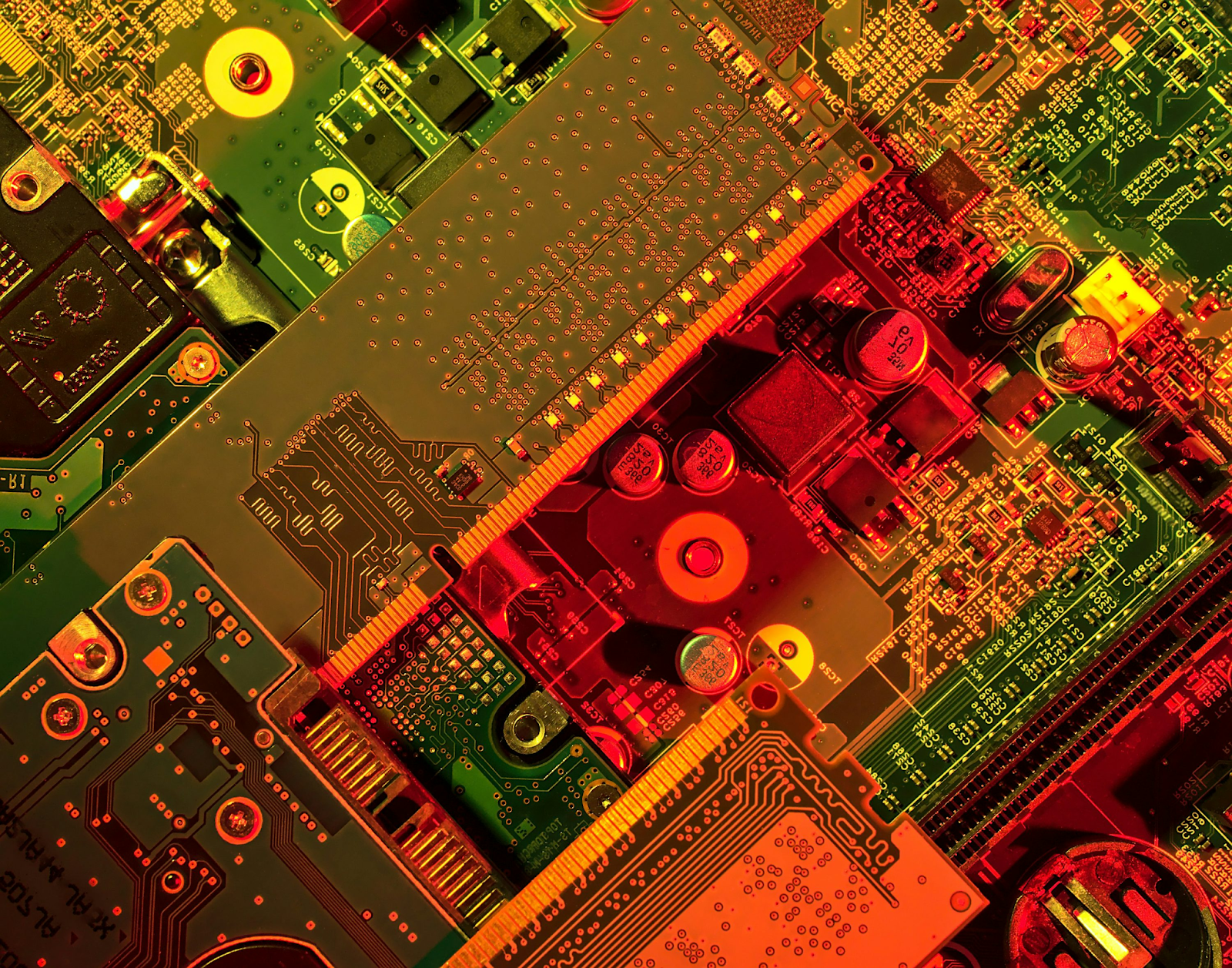
Gamers have uncovered a hardware-based exploit that boosts system performance beyond normal operating limits, affecting competitive gameplay and bypassing anti-cheat systems. Developers and hardware manufacturers are urgently investigating as esports leagues debate legality and fair-play implications. This article breaks down the exploit’s origins, impacts, ethics, and future consequences for gaming security and performance.
For years, software-based cheating was the primary concern for game developers. From wallhacks to aimbots to packet manipulation, almost every form of gaming exploit has been code-based. Developers responded by building stronger anti-cheat tools and real-time detection systems. But now, a new threat has emerged — and this time, it doesn’t live in the software layer at all.
Gamers have discovered a hardware-level exploit that manipulates performance timing between CPU, GPU, and memory components in ways that software can’t regulate or detect. Unlike typical overclocking or tuning, this exploit pushes hardware into execution states that the OS and game engines cannot accurately measure. Suddenly, some players are operating with a literal invisible advantage — and developers are scrambling behind the scenes.

What Exactly Is the Hardware Exploit?
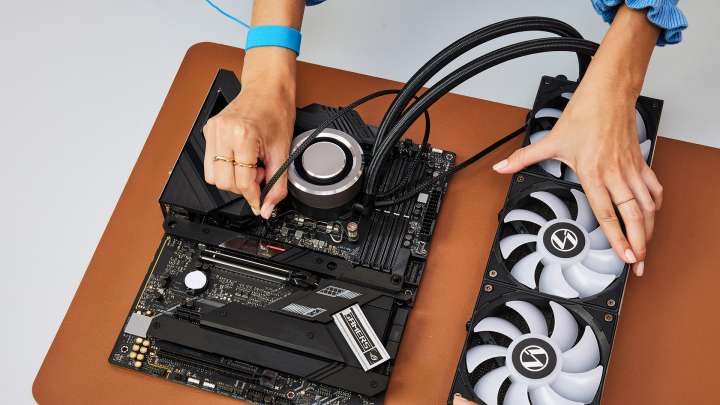
In simple terms, this exploit uses a combination of:
- Low-level motherboard firmware modification
- Non-standard memory timing overrides
- Custom interface controllers
- Microcode execution loopholes
Gamers have reportedly achieved:
- 23–30% higher framerates in GPU-bound titles
- 8–12 ms lower input latency in competitive shooters
- More responsive UI and reaction handling
- Faster internal physics computation
And here’s the worst part for developers:
Games perceive these enhanced outcomes as legitimate hardware performance, not as artificially manipulated execution timing.
That’s what makes it undetectable.
Is This Just Overclocking? Not Even Close
Overclocking is a known, documented, and controlled process. Hardware reports its boosted state, regulators monitor voltage and clock ceilings, and user risk factors are transparent.
But this exploit goes underneath:
- Instead of boosting clock speeds — it manipulates timing priority
- Instead of raising power — it bypasses regulation
- Instead of being visible — it masks itself as normal operations
Where overclocking modifies how fast hardware works,
this exploit modifies how soon tasks are processed.
The difference is subtle, but game-changing.
Why Developers Are Freaking Out
Game engines — especially competitive shooters — are built on assumptions of timing consistency. For example:
- If two players fire a bullet simultaneously
- If two movement commands are issued at the same time
- If two physics responses are triggered concurrently
Games assume synchronized processing.
But with the exploit:
- One player’s input reaches CPU earlier
- One GPU renders a frame ahead of schedule
- One networking stack finalizes data faster
That results in the equivalent of digital reaction cheating without actually modifying game code.
Imagine two players rounding a corner —
The player with the exploit literally sees the other first.
Milliseconds matter — and this grants them dozens.
Real-World Cases & Examples
Several gaming communities have reported unusual performance disparities:
Example 1: CS2 Competitive
Two identical PCs are benchmarked. Same GPU, same CPU, same settings — yet one player consistently sees up to +40 FPS and improved hit confirmation.
Example 2: Valorant Ranked
Players with the exploit achieve microsecond-level reduced firing response times — meaning in a close gun duel, they consistently land the first hit.
Example 3: Fortnite
Movement physics feel “lighter,” granting improved jump arcs and directional changes at competitive speeds.
These aren’t subjective impressions — high-speed analytics tools verified measurable and repeatable advantages.
The Bigger Problem: Anti-Cheat Can’t See It
Anti-cheat engines (BattleEye, Vanguard, Easy Anti-Cheat) monitor:
- Running processes
- Memory injection
- DLL tampering
- Packet spoofing
- In-game anomalies
But this exploit lives:
- Below the OS
- Below the drivers
- Below the kernel
- Below user-level programming
The exploit operates at BIOS/firmware/microcode level.
Which means:
- Anti-cheat sees nothing suspicious
- Games think everything is normal
- Servers see honest player inputs
- Esports oversight tools detect no cheating
In other words:
It’s invisible.
Why Esports Organizations Are Alarmed
Imagine the NFL allowed some players to run 20% faster because of a muscle implant — and referees could never detect it.
That’s how esports teams feel right now.
We may soon see:
- Mandatory tournament hardware
- Firmware validation locks
- Live telemetry input monitoring
- Standardized latency policies
- Pre-match physical device inspection
Like Formula 1 and NASCAR, esports may require hardware scrutineering.
Which Hardware Is Vulnerable?
Current findings point to:
- Unlocked Intel desktop CPUs
- Ryzen enthusiast series
- DDR5 memory with aggressive timing flexibility
- Custom XMP profiles
- Modified GPU firmware
- Motherboards supporting unofficial voltage modes
Interestingly:
- Gaming laptops are less vulnerable
- Consoles are even more secure
Because those systems enforce strict hardware standardization.
Ironically, PC gamers with high-end modular components are at the greatest risk.
Is It Dangerous for the Hardware?
Yes — misuse can damage components.
Cases include:
- Fried VRM circuits
- GPU fan overdrive
- Memory corruption at boot
- CPU clock instability
- Permanent BIOS damage
Some users have literally bricked their motherboard.
That’s the dark side of the exploit.
Will Developers Fix This?
Not easily.
Games cannot control:
- CMOS-level timing
- Voltage rail prioritization
- Microcode synchronization
- Hardware pipeline sequencing
Software can be patched.
Silicon cannot.
Fixing this may require:
- New CPU designs
- Firmware safeguards
- Motherboard standardization
- Anti-anomaly performance telemetry
This isn’t a patch — it’s an engineering revolution.
What Gamers Should Do Now
For casual players:
- Don’t panic — this won’t break public matchmaking
- Don’t attempt exploits yourself
- Expect some players to have unfair advantages temporarily
For competitive players:
- Avoid firmware mods
- Respect tournament rules
- Preserve your reputation
For developers:
- Partner with hardware vendors
- Research timing verification
- Implement framerate integrity checks
- Study microcode authentication
Gaming security has officially entered the hardware era.
10 Frequently Asked Questions
1. Can the exploit be detected by anti-cheat?
Not currently. Anti-cheat operates above hardware timing layers and cannot see the modifications.
2. Is this technically considered cheating?
It’s a gray area — currently legal in casual play, but expected to be banned in esports contexts.
3. Can consoles like Xbox or PlayStation be affected?
Unlikely. Their firmware architecture is locked and tightly controlled.
4. Is this risky to use on my PC?
Yes — incorrect usage can permanently damage components.
5. How much performance gain can it provide?
Reported gains range from 20–30% in framerate and 8–12ms in latency differences.
6. Will future hardware prevent these exploits?
Manufacturers will likely implement stricter timing enforcement in future chipsets.
7. Why is this especially bad for competitive shooters?
Milliseconds decide reaction time — tiny timing advantages can determine match outcomes.
8. Are developers acknowledging the issue publicly?
Not yet — most discussions appear to be happening internally and privately.
9. Should I be worried as a normal gamer?
No — this mostly affects high-level competitive gaming and leaderboards.
10. Will using this exploit get players banned later?
Possibly — if tournaments or platforms retroactively classify it as a violation.
Final Thoughts
This marks a turning point for gaming security. The battlefield is no longer just in code or software integrity — it is now inside the circuitry of the machine. Developers must evolve, esports must adapt, and gamers must understand that the future of competitive gaming may require physical hardware verification, not just software monitoring.
We are entering an era where milliseconds aren’t just technical — they are competitive currency.